Hello Guys, In this post we are going to disscuss about the file /etc/shadow. To change the password of the user on linux system we use the command ‘passwd‘, But on /etc/passwd file we don’t find any password details of
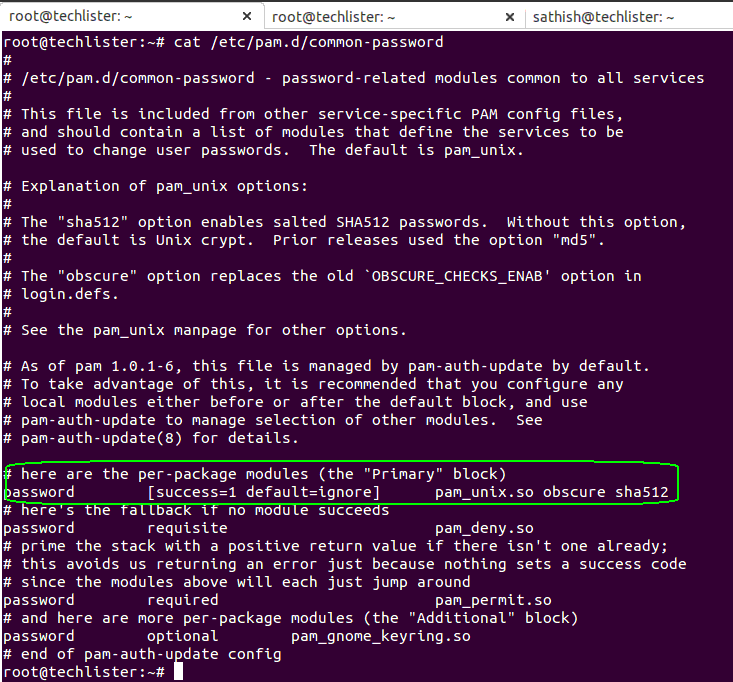
Linux : How to change the Password Hashing Algorithm on linux system